Module 13 computer concepts exam – Embark on a comprehensive journey through Module 13 of the Computer Concepts Exam, where you will delve into the fundamentals of networking, unravel the intricacies of network security, explore the transformative power of cloud computing, and discover the cutting-edge technologies shaping the future of computing.
This module promises an immersive learning experience, equipping you with a solid understanding of the concepts and technologies that underpin modern computing.
Module 13 Overview
Module 13 delves into the intricacies of computer networks, exploring the fundamental concepts, protocols, and architectures that underpin the interconnected world we rely on today.
This module aims to equip learners with a comprehensive understanding of network topologies, transmission media, network devices, and the essential protocols that facilitate data communication across networks.
Network Topologies
Network topologies refer to the physical and logical arrangements of devices within a network. Common topologies include:
- Bus Topology
- Ring Topology
- Star Topology
- Mesh Topology
- Hybrid Topology
Transmission Media
Transmission media refers to the physical channels through which data signals travel in a network. Types of transmission media include:
- Twisted Pair Cables
- Coaxial Cables
- Fiber Optic Cables
- Wireless Media
Network Devices
Network devices play crucial roles in facilitating data communication and network management. Key network devices include:
- Network Interface Cards (NICs)
- Routers
- Switches
- Modems
- Firewalls
Network Protocols
Network protocols define the rules and procedures that govern data communication across networks. Essential protocols include:
- Transmission Control Protocol (TCP)
- Internet Protocol (IP)
- Hypertext Transfer Protocol (HTTP)
- File Transfer Protocol (FTP)
Networking Fundamentals
Computer networks are a vital part of our modern world, connecting devices and allowing them to communicate and share resources. Understanding the basic concepts of networking is essential for anyone who uses computers.
Types of Networks
There are many different types of networks, each with its own characteristics and purposes. Some of the most common types of networks include:
- Local Area Networks (LANs)are small networks that connect devices within a limited area, such as a home or office.
- Wide Area Networks (WANs)are larger networks that connect devices over a wide geographic area, such as a country or continent.
- Metropolitan Area Networks (MANs)are networks that connect devices within a metropolitan area, such as a city.
- Virtual Private Networks (VPNs)are networks that use encryption to create a secure connection between devices over a public network, such as the Internet.
Components of a Network
Networks are made up of a variety of hardware and software components. Some of the most common components include:
- Network Interface Cards (NICs)are devices that allow computers to connect to a network.
- Routersare devices that direct traffic between different networks.
- Switchesare devices that connect multiple devices to a network.
- Firewallsare devices that protect networks from unauthorized access.
- Network operating systems (NOSs)are software that manages and controls networks.
Network Topologies
The topology of a network refers to the way that the devices in the network are connected. There are a variety of different network topologies, each with its own advantages and disadvantages.
| Topology | Advantages | Disadvantages |
|---|---|---|
| Bus |
|
|
| Ring |
|
|
| Star |
|
|
| Mesh |
|
|
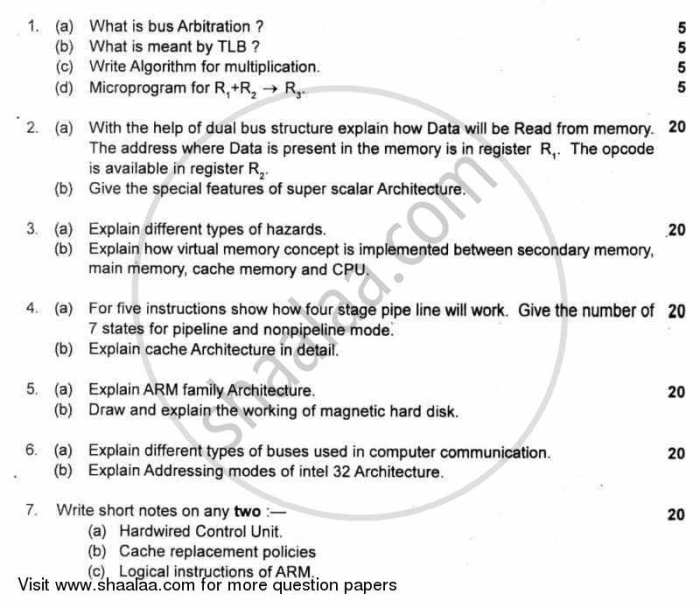
Network Security
Network security is of paramount importance in today’s digital world, where networks are increasingly interconnected and vulnerable to cyber threats. It involves the protection of computer networks from unauthorized access, misuse, disruption, modification, or destruction of information.Network security threats can originate from both external and internal sources.
External threats include hackers, malware, phishing attacks, and denial-of-service attacks. Internal threats can arise from malicious insiders, unintentional errors, or inadequate security measures.
Common Network Security Threats and Vulnerabilities
-
-*Malware
Malicious software, such as viruses, worms, and Trojans, can infect and damage computers, steal data, and spread to other devices on the network.
-*Phishing attacks
Fraudulent emails or websites attempt to trick users into revealing sensitive information, such as passwords or financial data.
-*Denial-of-service attacks
These attacks flood a network with excessive traffic, making it unavailable to legitimate users.
-*Buffer overflow
A vulnerability that allows attackers to execute malicious code by overflowing a memory buffer.
-*SQL injection
An attack that exploits vulnerabilities in database systems to inject malicious SQL commands.
Security Measures to Protect Networks
-
-*Firewalls
Hardware or software that monitors and controls incoming and outgoing network traffic, blocking unauthorized access.
-*Intrusion detection systems (IDS)
Monitor network traffic for suspicious activity and alert administrators to potential threats.
-*Antivirus software
Scans files and emails for malicious software and prevents its execution.
-*Encryption
Converts data into an unreadable format to protect it from unauthorized access.
-*Multi-factor authentication
Requires users to provide multiple forms of identification to access sensitive data or systems.
Cryptography in Network Security
Cryptography plays a crucial role in network security by providing confidentiality, integrity, and authenticity. Confidentiality ensures that data is accessible only to authorized parties, while integrity guarantees that data has not been altered. Authenticity verifies the identity of the sender and ensures that the message has not been tampered with.Common
cryptographic techniques include:
-
-*Symmetric-key cryptography
Uses the same key for encryption and decryption.
-*Asymmetric-key cryptography
Uses different keys for encryption and decryption.
-*Hash functions
Create a unique and irreversible fingerprint of a data set.
-*Digital signatures
Electronically signed documents that verify the authenticity and integrity of the signer.
Cloud Computing
Cloud computing refers to the on-demand delivery of IT resources and applications over the internet, typically on a pay-as-you-go basis. It provides businesses with access to scalable, flexible, and cost-effective computing resources without the need for extensive in-house infrastructure.Cloud computing offers numerous benefits, including:
-
-*Scalability
Cloud resources can be scaled up or down quickly to meet changing business demands.
-*Flexibility
Cloud services can be customized to meet specific business requirements.
-*Cost-effectiveness
Businesses only pay for the resources they use, eliminating the need for large upfront investments in hardware and software.
-*Reliability
Cloud providers offer high levels of uptime and redundancy to ensure service availability.
-*Accessibility
Cloud services can be accessed from anywhere with an internet connection.
Cloud Computing Models
There are three main cloud computing models:
-
-*Public cloud
Public clouds are shared infrastructure and resources provided by third-party vendors. They offer the highest level of scalability and flexibility but may not provide the same level of security and control as private clouds.
-*Private cloud
Private clouds are dedicated infrastructure and resources for a single organization. They provide the highest level of security and control but may be more expensive and less scalable than public clouds.
-*Hybrid cloud
Hybrid clouds combine public and private clouds, allowing businesses to take advantage of the benefits of both models.
Applications of Cloud Computing
Cloud computing has a wide range of applications, including:
-
-*Software as a Service (SaaS)
SaaS providers deliver software applications over the internet, eliminating the need for businesses to install and maintain software on their own systems.
-*Platform as a Service (PaaS)
PaaS providers offer a platform for businesses to develop, deploy, and manage their own applications.
-*Infrastructure as a Service (IaaS)
IaaS providers offer infrastructure, such as servers, storage, and networking, on a pay-as-you-go basis.
Cloud Computing Services and Providers
There are numerous cloud computing services and providers available, including:
-
-*Amazon Web Services (AWS)
AWS is the largest cloud provider, offering a wide range of services, including IaaS, PaaS, and SaaS.
-*Microsoft Azure
Microsoft Azure is a comprehensive cloud platform that provides a range of services, including IaaS, PaaS, and SaaS.
-*Google Cloud Platform (GCP)
GCP offers a range of cloud services, including IaaS, PaaS, and SaaS, with a focus on artificial intelligence and machine learning.
Comparison of Cloud Computing Models
The following table compares the advantages and disadvantages of public, private, and hybrid cloud models:| Cloud Model | Advantages | Disadvantages ||—|—|—||
*Public Cloud | Scalable, flexible, cost-effective | Limited security and control, data privacy concerns |
|
*Private Cloud | High security and control, dedicated resources | Expensive, less scalable |
|
*Hybrid Cloud | Combines benefits of public and private clouds | Can be complex to manage, potential security risks |
Data Management: Module 13 Computer Concepts Exam
Data management encompasses the practices and techniques used to handle data throughout its lifecycle, ensuring its accuracy, consistency, and accessibility. It involves data collection, storage, organization, analysis, and protection.
Effective data management is crucial for organizations to make informed decisions, optimize operations, and maintain data integrity. It enables businesses to derive valuable insights from their data, gain a competitive edge, and comply with regulatory requirements.
Types of Databases
Databases are essential for organizing and managing large volumes of data. Different types of databases exist, each suited for specific applications:
- Relational databases: Store data in tables with rows and columns, allowing for efficient data retrieval and manipulation using Structured Query Language (SQL).
- NoSQL databases: Designed for handling unstructured or semi-structured data, offering flexibility and scalability for modern applications.
- Cloud databases: Hosted on remote servers, providing scalability, reliability, and cost-effectiveness for data storage and management.
Data Integrity, Consistency, and Security, Module 13 computer concepts exam
Data integrity refers to the accuracy and completeness of data, while data consistency ensures that data is consistent across different systems and applications.
Data security measures protect data from unauthorized access, modification, or destruction. Common security measures include encryption, access controls, and data backup and recovery.
Database Schema Design
A database schema is a blueprint that defines the structure and relationships of data within a database. It determines how data is organized, stored, and accessed.
When designing a database schema, it is important to consider the following:
- Data requirements and relationships
- Data integrity and consistency constraints
- Performance and scalability considerations
Emerging Technologies
Emerging technologies are rapidly evolving and transforming various industries, driving innovation and creating new possibilities. These technologies encompass a wide range of advancements, including artificial intelligence (AI), blockchain, cloud computing, and quantum computing.
The potential impact of emerging technologies is vast, affecting sectors such as healthcare, finance, manufacturing, and transportation. These technologies have the power to automate tasks, improve efficiency, enhance decision-making, and foster new levels of collaboration and connectivity.
Artificial Intelligence
AI involves the development of intelligent systems that can perform tasks that typically require human intelligence, such as learning, problem-solving, and decision-making. AI technologies are being used in a variety of applications, including:
- Natural language processing (NLP) for understanding and generating human language.
- Machine learning (ML) for training computers to learn from data without explicit programming.
- Computer vision for enabling computers to interpret and analyze visual information.
FAQ Guide
What are the key topics covered in Module 13 of the Computer Concepts Exam?
Module 13 encompasses networking fundamentals, network security, cloud computing, data management, and emerging technologies.
What are the benefits of cloud computing discussed in the module?
The module highlights the benefits of cloud computing, including scalability, cost-effectiveness, and flexibility.
What emerging technologies are explored in the module?
The module examines emerging technologies such as artificial intelligence, blockchain, and quantum computing, discussing their potential impact on various industries.